With the widespread consideration, and potential purposes of blockchain and synthetic intelligence applied sciences, the privateness safety methods that come up as a direct results of integration of the 2 applied sciences is gaining notable significance. These privateness safety methods not solely shield the privateness of people, however additionally they assure the dependability and safety of the info.
On this article, we can be speaking about how the collaboration between AI and blockchain offers beginning to quite a few privateness safety methods, and their utility in numerous verticals together with de-identification, knowledge encryption, k-anonymity, and multi-tier distributed ledger strategies. Moreover, we may also attempt to analyze the deficiencies together with their precise trigger, and provide options accordingly.
The blockchain community was first launched to the world when in 2008 Nakamoto launched Bitcoin, a cryptocurrency constructed on the blockchain community. Ever since its introduction, blockchain has gained plenty of recognition, particularly previously few years. The worth at which Bitcoin is buying and selling at present, and it crossing the Trillion-dollar market cap mark signifies that blockchain has the potential to generate substantial income and earnings for the business.
Blockchain expertise might be categorized totally on the idea of the extent of accessibility and management they provide, with Public, Personal, and Federated being the three primary varieties of blockchain applied sciences. Standard cryptocurrencies and blockchain architectures like Bitcoin and Ethereum are public blockchain choices as they’re decentralized in nature, they usually permit nodes to enter or exit the community freely, and thus promotes most decentralization.
The next determine depicts the construction of Ethereum because it makes use of a linked listing to ascertain connections between completely different blocks. The header of the block shops the hash handle of the previous block so as to set up a linkage between the 2 successive blocks.
The event, and implementation of the blockchain expertise is adopted with reliable safety and privateness considerations in varied fields that can not be uncared for. For instance, an information breach within the monetary business may end up in heavy losses, whereas a breach in navy or healthcare programs might be disastrous. To forestall these situations, safety of knowledge, person property, and id data has been a significant focus of the blockchain safety analysis group, as to make sure the event of the blockchain expertise, it’s important to take care of its safety.
Ethereum is a decentralized blockchain platform that upholds a shared ledger of knowledge collaboratively utilizing a number of nodes. Every node within the Ethereum community makes use of the EVM or Ethereum Vector Machine to compile sensible contracts, and facilitate the communication between nodes that happen by way of a P2P or peer-to-peer community. Every node on the Ethereum community is supplied with distinctive capabilities, and permissions, though all of the nodes can be utilized for gathering transactions, and interesting in block mining. Moreover, it’s value noting that when in comparison with Bitcoin, Ethereum shows sooner block era speeds with a lead of practically 15 seconds. It signifies that crypto miners have a greater likelihood at buying rewards faster whereas the interval time for verifying transactions is decreased considerably.
Alternatively, AI or Synthetic Intelligence is a department in trendy science that focuses on creating machines which might be able to decision-making, and may simulate autonomous considering corresponding to a human’s skill. Synthetic Intelligence is a really huge department in itself with quite a few subfields together with deep studying, pc imaginative and prescient, pure language processing, and extra. NLP specifically has been a subfield that has been focussed closely previously few years that has resulted within the growth of some top-notch LLMs like GPT and BERT. NLP is headed in direction of close to perfection, and the ultimate step of NLP is processing textual content transformations that may make computer systems comprehensible, and up to date fashions like ChatGPT constructed on GPT-4 indicated that the analysis is headed in direction of the appropriate course.
One other subfield that’s fairly common amongst AI builders is deep studying, an AI approach that works by imitating the construction of neurons. In a standard deep studying framework, the exterior enter data is processed layer by layer by coaching hierarchical community buildings, and it’s then handed on to a hidden layer for closing illustration. Deep studying frameworks might be labeled into two classes: Supervised studying, and Unsupervised studying.

The above picture depicts the structure of deep studying perceptron, and as it may be seen within the picture, a deep studying framework employs a multiple-level neural community structure to be taught the options within the knowledge. The neural community consists of three varieties of layers together with the hidden layer, the enter payer, and the output layer. Every perceptron layer within the framework is linked to the subsequent layer so as to type a deep studying framework.
Lastly, we’ve got the combination of blockchain and synthetic intelligence applied sciences as these two applied sciences are being utilized throughout completely different industries and domains with a rise within the concern relating to cybersecurity, knowledge safety, and privateness safety. Functions that goal to combine blockchain and synthetic intelligence manifest the combination within the following points.
- Using blockchain expertise to report and retailer the coaching knowledge, enter and output of the fashions, and parameters, guaranteeing accountability, and transparency in mannequin audits.
- Utilizing blockchain frameworks to deploy AI fashions to realize decentralization providers amongst fashions, and enhancing the scalability and stability of the system.
- Offering safe entry to exterior AI knowledge and fashions utilizing decentralized programs, and enabling blockchain networks to accumulate exterior data that’s dependable.
- Utilizing blockchain-based token designs and incentive mechanisms to ascertain connections and trust-worthy interactions between customers and AI mannequin builders.
Privateness Safety By the Integration of Blockchain and AI Applied sciences
Within the present situation, knowledge belief programs have sure limitations that compromise the reliability of the info transmission. To problem these limitations, blockchain applied sciences might be deployed to ascertain a reliable and safe knowledge sharing & storage resolution that provides privateness safety, and enhances knowledge safety. A few of the purposes of blockchain in AI privateness safety are talked about within the following desk.
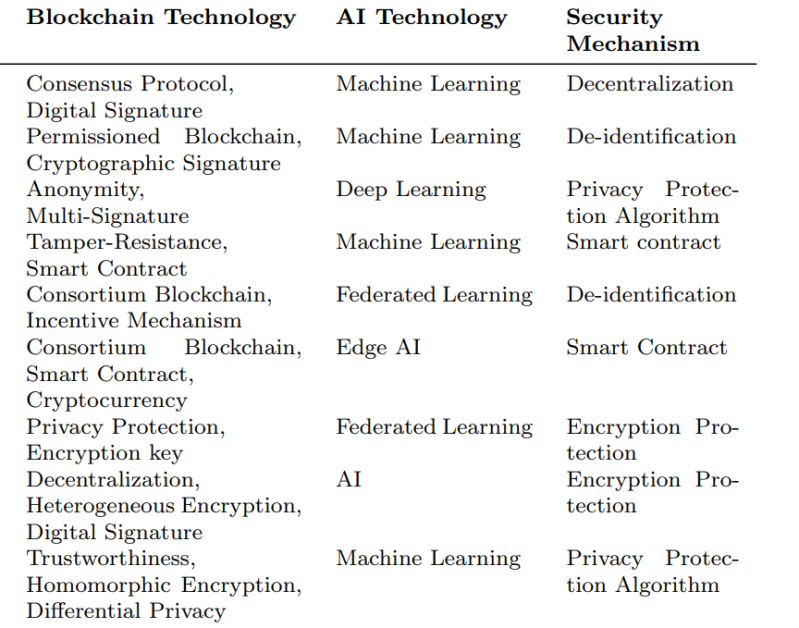
By enhancing the implementation & integration of those applied sciences, the protecting capability & safety of present knowledge belief programs might be boosted considerably.
Information Encryption
Historically, knowledge sharing and knowledge storing strategies have been weak to safety threats as a result of they’re depending on centralized servers that makes them an simply identifiable goal for attackers. The vulnerability of those strategies offers rise to severe problems reminiscent of knowledge tampering, and knowledge leaks, and given the present safety necessities, encryption strategies alone should not ample to make sure the protection & safety of the info, which is the principle cause behind the emergence of privateness safety applied sciences based mostly on the combination of synthetic intelligence & blockchain.
Let’s take a look at a blockchain-based privateness preserving federated studying scheme that goals to enhance the Multi-Krum approach, and mix it with homomorphic encryption to realize ciphertext-level mannequin filtering and mannequin aggregation that may confirm native fashions whereas sustaining privateness safety. The Paillier homomorphic encryption approach is used on this technique to encrypt mannequin updates, and thus offering further privateness safety. The Paillier algorithm works as depicted.

De-Identification
De-Identification is a technique that’s generally used to anonymize private identification data of a person within the knowledge by separating the info from the info identifiers, and thus decreasing the chance of knowledge monitoring. There exists a decentralized AI framework constructed on permissioned blockchain expertise that makes use of the above talked about method. The AI framework basically separates the private identification data from non-personal data successfully, after which shops the hash values of the private identification data within the blockchain community. The proposed AI framework might be utilized within the medical business to share medical information & data of a affected person with out revealing his/her true id. As depicted within the following picture, the proposed AI framework makes use of two unbiased blockchain for knowledge requests with one blockchain community storing the affected person’s data together with knowledge entry permissions whereas the second blockchain community captures audit traces of any requests or queries made by requesters. Consequently, sufferers nonetheless have full authority and management over their medical information & delicate data whereas enabling safe & secure knowledge sharing inside a number of entities on the community.
Multi-Layered Distributed Ledger
A multi-layered distributed ledger is an information storage system with decentralization property and a number of hierarchical layers which might be designed to maximise effectivity, and safe the info sharing course of together with enhanced privateness safety. DeepLinQ is a blockchain-based multi-layered decentralized distributed ledger that addresses a person’s concern relating to knowledge privateness & knowledge sharing by enabling privacy-protected knowledge privateness. DeepLinQ archives the promised knowledge privateness by using varied methods like on-demand querying, entry management, proxy reservation, and sensible contracts to leverage blockchain community’s traits together with consensus mechanism, full decentralization, and anonymity to guard knowledge privateness.
Ok-Anonymity
The Ok-Anonymity technique is a privateness safety technique that goals to focus on & group people in a dataset in a manner that each group has not less than Ok people with similar attribute values, and due to this fact defending the id & privateness of particular person customers. The Ok-Anonymity technique has been the idea of a proposed dependable transactional mannequin that facilitates transactions between vitality nodes, and electrical automobiles. On this mannequin, the Ok-Anonymity technique serves two capabilities: first, it hides the situation of the EVs by developing a unified request utilizing Ok-Anonymity methods that conceal or conceal the situation of the proprietor of the automobile; second, the Ok-Anonymity technique conceals person identifiers in order that attackers should not left with the choice to hyperlink customers to their electrical automobiles.
Analysis and State of affairs Evaluation
On this part, we can be speaking about complete evaluation and analysis of ten privateness safety programs utilizing the fusion of blockchain and AI applied sciences which were proposed lately. The analysis focuses on 5 main traits of those proposed strategies together with: authority administration, knowledge safety, entry management, scalability and community safety, and likewise discusses the strengths, weaknesses, and potential areas of enchancment. It is the distinctive options ensuing from the combination of AI and blockchain applied sciences which have paved methods for brand new concepts, and options for enhanced privateness safety. For reference, the picture beneath reveals completely different analysis metrics employed to derive the analytical outcomes for the mixed utility of the blockchain and AI applied sciences.

Authority Administration
Entry management is a safety & privateness expertise that’s used to limit a person’s entry to licensed assets on the idea of pre-defined guidelines, set of directions, insurance policies, safeguarding knowledge integrity, and system safety. There exists an clever privateness parking administration system that makes use of a Position-Based mostly Entry Management or RBAC mannequin to handle permissions. Within the framework, every person is assigned a number of roles, and are then labeled in response to roles that enables the system to manage attribute entry permissions. Customers on the community could make use of their blockchain handle to confirm their id, and get attribute authorization entry.
Entry Management
Entry management is likely one of the key fundamentals of privateness safety, proscribing entry based mostly on group membership & person id to make sure that it’s only the licensed customers who can entry particular assets that they’re allowed to entry, and thus defending the system from undesirable to compelled entry. To make sure efficient and environment friendly entry management, the framework wants to think about a number of elements together with authorization, person authentication, and entry insurance policies.
Digital Identification Expertise is an rising method for IoT purposes that may present secure & safe entry management, and guarantee knowledge & gadget privateness. The tactic proposes to make use of a collection of entry management insurance policies which might be based mostly on cryptographic primitives, and digital id expertise or DIT to guard the safety of communications between entities reminiscent of drones, cloud servers, and Floor Station Servers (GSS). As soon as the registration of the entity is accomplished, credentials are saved within the reminiscence. The desk included beneath summarizes the varieties of defects within the framework.

Information Safety
Information safety is used to consult with measures together with knowledge encryption, entry management, safety auditing, and knowledge backup to make sure that the info of a person will not be accessed illegally, tampered with, or leaked. In the case of knowledge processing, applied sciences like knowledge masking, anonymization, knowledge isolation, and knowledge encryption can be utilized to guard knowledge from unauthorized entry, and leakage. Moreover, encryption applied sciences reminiscent of homomorphic encryption, differential privateness safety, digital signature algorithms, uneven encryption algorithms, and hash algorithms, can stop unauthorized & unlawful entry by non-authorized customers and guarantee knowledge confidentiality.
Community Safety
Community safety is a broad area that encompasses completely different points together with guaranteeing knowledge confidentiality & integrity, stopping community assaults, and defending the system from community viruses & malicious software program. To make sure the protection, reliability, and safety of the system, a collection of safe community architectures and protocols, and safety measures should be adopted. Moreover, analyzing and assessing varied community threats and developing with corresponding protection mechanisms and safety methods are important to enhance the reliability & safety of the system.

Scalability
Scalability refers to a system’s skill to deal with bigger quantities of knowledge or an rising variety of customers. When designing a scalable system, builders should take into account system efficiency, knowledge storage, node administration, transmission, and several other different elements. Moreover, when guaranteeing the scalability of a framework or a system, builders should take into consideration the system safety to stop knowledge breaches, knowledge leaks, and different safety dangers.
Builders have designed a system in compliance with European Common Information Safety Guidelines or GDPR by storing privacy-related data, and paintings metadata in a distributed file system that exists off the chain. Paintings metadata and digital tokens are saved in OrbitDB, a database storage system that makes use of a number of nodes to retailer the info, and thus ensures knowledge safety & privateness. The off-chain distributed system disperses knowledge storage, and thus improves the scalability of the system.

State of affairs Evaluation
The amalgamation of AI and blockchain applied sciences has resulted in creating a system that focuses closely on defending the privateness, id, and knowledge of the customers. Though AI knowledge privateness programs nonetheless face some challenges like community safety, knowledge safety, scalability, and entry management, it’s essential to think about and weigh these points on the idea of sensible concerns in the course of the design part comprehensively. Because the expertise develops and progresses additional, the purposes develop, the privateness safety programs constructed utilizing AI & blockchain will draw extra consideration within the upcoming future. On the idea of analysis findings, technical approaches, and utility situations, they are often labeled into three classes.
- Privateness safety technique utility within the IoT or Web of Issues business by using each blockchain and AI expertise.
- Privateness safety technique utility in sensible contract and providers that make use of each blockchain and AI expertise.
- Massive-scale knowledge evaluation strategies that provide privateness safety by using each blockchain and AI expertise.
The applied sciences belonging to the primary class give attention to the implementation of AI and blockchain applied sciences for privateness safety within the IoT business. These strategies use AI methods to research excessive volumes of knowledge whereas making the most of decentralized & immutable options of the blockchain community to make sure authenticity and safety of the info.
The applied sciences falling within the second class give attention to fusing AI & Blockchain applied sciences for enhanced privateness safety by making use of blockchain’s sensible contract & providers. These strategies mix knowledge evaluation and knowledge processing with AI and use blockchain expertise alongside to cut back dependency on trusted third events, and report transactions.
Lastly, the applied sciences falling within the third class give attention to harnessing the facility of AI and blockchain expertise to realize enhanced privateness safety in large-scale knowledge analytics. These strategies goal to take advantage of blockchain’s decentralization, and immutability properties that make sure the authenticity & safety of knowledge whereas AI methods make sure the accuracy of knowledge evaluation.
Conclusion
On this article, we’ve got talked about how AI and Blockchain applied sciences can be utilized in sync with one another to reinforce the purposes of privateness safety applied sciences by speaking about their associated methodologies, and evaluating the 5 major traits of those privateness safety applied sciences. Moreover, we’ve got additionally talked concerning the present limitations of the present programs. There are specific challenges within the area of privateness safety applied sciences constructed upon blockchain and AI that also should be addressed like learn how to strike a steadiness between knowledge sharing, and privateness preservation. The analysis on learn how to successfully merge the capabilities of AI and Blockchain methods is happening, and listed here are a number of different ways in which can be utilized to combine different methods.
Edge computing goals to realize decentralization by leveraging the facility of edge & IoT gadgets to course of non-public & delicate person knowledge. As a result of AI processing makes it necessary to make use of substantial computing assets, utilizing edge computing strategies can allow the distribution of computational duties to edge gadgets for processing as an alternative of migrating the info to cloud providers, or knowledge servers. Because the knowledge is processed a lot nearer the sting gadget itself, the latency time is decreased considerably, and so is the community congestion that enhances the velocity & efficiency of the system.
Multi-chain mechanisms have the potential to resolve single-chain blockchain storage, and efficiency points, due to this fact boosting the scalability of the system. The mixing of multi-chain mechanisms facilitates distinct attributes & privacy-levels based mostly knowledge classification, due to this fact enhancing storage capabilities and safety of privateness safety programs.