Though the deepfaking of personal people has change into a rising public concern and is more and more being outlawed in varied areas, really proving {that a} user-created mannequin – corresponding to one enabling revenge porn – was particularly educated on a selected particular person’s pictures stays extraordinarily difficult.
To place the issue in context: a key factor of a deepfake assault is falsely claiming that a picture or video depicts a particular particular person. Merely stating that somebody in a video is id #A, relatively than only a lookalike, is sufficient to create hurt, and no AI is critical on this state of affairs.
Nonetheless, if an attacker generates AI pictures or movies utilizing fashions educated on actual particular person’s information, social media and search engine face recognition techniques will routinely hyperlink the faked content material to the sufferer –with out requiring names in posts or metadata. The AI-generated visuals alone make sure the affiliation.
The extra distinct the particular person’s look, the extra inevitable this turns into, till the fabricated content material seems in picture searches and in the end reaches the sufferer.
Face to Face
The most typical technique of disseminating identity-focused fashions is presently via Low-Rank Adaptation (LoRA), whereby the person trains a small variety of pictures for a number of hours in opposition to the weights of a far bigger basis mannequin corresponding to Steady Diffusion (for static pictures, largely) or Hunyuan Video, for video deepfakes.
The most typical targets of LoRAs, together with the brand new breed of video-based LoRAs, are feminine celebrities, whose fame exposes them to this type of therapy with much less public criticism than within the case of ‘unknown’ victims, because of the assumption that such by-product works are lined underneath ‘truthful use’ (not less than within the USA and Europe).
Feminine celebrities dominate the LoRA and Dreambooth listings on the civit.ai portal. The preferred such LoRA presently has greater than 66,000 downloads, which is appreciable, provided that this use of AI stays seen as a ‘fringe’ exercise.
There isn’t any such public discussion board for the non-celebrity victims of deepfaking, who solely floor within the media when prosecution circumstances come up, or the victims communicate out in in style retailers.
Nonetheless, in each eventualities, the fashions used to faux the goal identities have ‘distilled’ their coaching information so utterly into the latent house of the mannequin that it’s tough to establish the supply pictures that have been used.
If it have been attainable to take action inside a suitable margin of error, this may allow the prosecution of those that share LoRAs, because it not solely proves the intent to deepfake a selected id (i.e., that of a specfic ‘unknown’ particular person, even when the malefactor by no means names them in the course of the defamation course of), but additionally exposes the uploader to copyright infringement costs, the place relevant.
The latter could be helpful in jurisdictions the place authorized regulation of deepfaking applied sciences is missing or lagging behind.
Over-Uncovered
The target of coaching a basis mannequin, such because the multi-gigabyte base mannequin {that a} person may obtain from Hugging Face, is that the mannequin ought to change into well-generalized, and ductile. This entails coaching on an satisfactory variety of numerous pictures, and with applicable settings, and ending coaching earlier than the mannequin ‘overfits’ to the info.
An overfitted mannequin has seen the info so many (extreme) instances in the course of the coaching course of that it’ll have a tendency to breed pictures which can be very comparable, thereby exposing the supply of coaching information.

The id ‘Ann Graham Lotz’ will be nearly completely reproduced within the Steady Diffusion V1.5 mannequin. The reconstruction is almost an identical to the coaching information (on the left within the picture above). Supply: https://arxiv.org/pdf/2301.13188
Nonetheless, overfitted fashions are typically discarded by their creators relatively than distributed, since they’re in any case unfit for function. Subsequently that is an unlikely forensic ‘windfall’. In any case, the precept applies extra to the costly and high-volume coaching of basis fashions, the place a number of variations of the identical picture which have crept into an enormous supply dataset could make sure coaching pictures straightforward to invoke (see picture and instance above).
Issues are a little bit totally different within the case of LoRA and Dreambooth fashions (although Dreambooth has fallen out of vogue attributable to its massive file sizes). Right here, the person selects a really restricted variety of numerous pictures of a topic, and makes use of these to coach a LoRA.

On the left, output from a Hunyuan Video LoRA. On the precise, the info that made the resemblance attainable (pictures used with permission of the particular person depicted).
Steadily the LoRA could have a trained-in trigger-word, corresponding to [nameofcelebrity]. Nonetheless, fairly often the specifically-trained topic will seem in generated output even with out such prompts, as a result of even a well-balanced (i.e., not overfitted) LoRA is considerably ‘fixated’ on the fabric it was educated on, and can have a tendency to incorporate it in any output.
This predisposition, mixed with the restricted picture numbers which can be optimum for a LoRA dataset, expose the mannequin to forensic evaluation, as we will see.
Unmasking the Information
These issues are addressed in a brand new paper from Denmark, which gives a strategy to establish supply pictures (or teams of supply pictures) in a black-box Membership Inference Assault (MIA). The method not less than partially entails using custom-trained fashions which can be designed to assist expose supply information by producing their very own ‘deepfakes’:

Examples of ‘faux’ pictures generated by the brand new method, at ever-increasing ranges of Classifier-Free Steering (CFG), as much as the purpose of destruction. Supply: https://arxiv.org/pdf/2502.11619
Although the work, titled Membership Inference Assaults for Face Photos Towards Positive-Tuned Latent Diffusion Fashions, is a most attention-grabbing contribution to the literature round this explicit matter, additionally it is an inaccessible and tersely-written paper that wants appreciable decoding. Subsequently we’ll cowl not less than the fundamental ideas behind the undertaking right here, and a choice of the outcomes obtained.
In impact, if somebody fine-tunes an AI mannequin in your face, the authors’ technique may help show it by on the lookout for telltale indicators of memorization within the mannequin’s generated pictures.
Within the first occasion, a goal AI mannequin is fine-tuned on a dataset of face pictures, making it extra more likely to reproduce particulars from these pictures in its outputs. Subsequently, a classifier assault mode is educated utilizing AI-generated pictures from the goal mannequin as ‘positives’ (suspected members of the coaching set) and different pictures from a distinct dataset as ‘negatives’ (non-members).
By studying the refined variations between these teams, the assault mannequin can predict whether or not a given picture was a part of the unique fine-tuning dataset.
The assault is handiest in circumstances the place the AI mannequin has been fine-tuned extensively, which means that the extra a mannequin is specialised, the better it’s to detect if sure pictures have been used. This typically applies to LoRAs designed to recreate celebrities or personal people.
The authors additionally discovered that including seen watermarks to coaching pictures makes detection simpler nonetheless – although hidden watermarks don’t assist as a lot.
Impressively, the method is examined in a black-box setting, which means it really works with out entry to the mannequin’s inside particulars, solely its outputs.
The strategy arrived at is computationally intense, because the authors concede; nevertheless, the worth of this work is in indicating the path for added analysis, and to show that information will be realistically extracted to a suitable tolerance; subsequently, given its seminal nature, it needn’t run on a smartphone at this stage.
Technique/Information
A number of datasets from the Technical College of Denmark (DTU, the host establishment for the paper’s three researchers) have been used within the examine, for fine-tuning the goal mannequin and for coaching and testing the assault mode.
Datasets used have been derived from DTU Orbit:
DseenDTU The bottom picture set.
DDTU Photos scraped from DTU Orbit.
DseenDTU A partition of DDTU used to fine-tune the goal mannequin.
DunseenDTU A partition of DDTU that was not used to fine-tune any picture era mannequin and was as an alternative used to check or practice the assault mannequin.
wmDseenDTU A partition of DDTU with seen watermarks used to fine-tune the goal mannequin.
hwmDseenDTU A partition of DDTU with hidden watermarks used to fine-tune the goal mannequin.
DgenDTU Photos generated by a Latent Diffusion Mannequin (LDM) which has been fine-tuned on the DseenDTU picture set.
The datasets used to fine-tune the goal mannequin include image-text pairs captioned by the BLIP captioning mannequin (maybe not by coincidence one of the in style uncensored fashions within the informal AI neighborhood).
BLIP was set to prepend the phrase ‘a dtu headshot of a’ to every description.
Moreover, a number of datasets from Aalborg College (AAU) have been employed within the checks, all derived from the AU VBN corpus:
DAAU Photos scraped from AAU vbn.
DseenAAU A partition of DAAU used to fine-tune the goal mannequin.
DunseenAAU A partition of DAAU that isn’t used to fine-tune any picture era mannequin, however relatively is used to check or practice the assault mannequin.
DgenAAU Photos generated by an LDM fine-tuned on the DseenAAU picture set.
Equal to the sooner units, the phrase ‘a aau headshot of a’ was used. This ensured that every one labels within the DTU dataset adopted the format ‘a dtu headshot of a (…)’, reinforcing the dataset’s core traits throughout fine-tuning.
Checks
A number of experiments have been performed to judge how properly the membership inference assaults carried out in opposition to the goal mannequin. Every take a look at aimed to find out whether or not it was attainable to hold out a profitable assault throughout the schema proven under, the place the goal mannequin is fine-tuned on a picture dataset that was obtained with out authorization.

Schema for the method.
With the fine-tuned mannequin queried to generate output pictures, these pictures are then used as constructive examples for coaching the assault mannequin, whereas extra unrelated pictures are included as destructive examples.
The assault mannequin is educated utilizing supervised studying and is then examined on new pictures to find out whether or not they have been initially a part of the dataset used to fine-tune the goal mannequin. To judge the accuracy of the assault, 15% of the take a look at information is put aside for validation.
As a result of the goal mannequin is fine-tuned on a identified dataset, the precise membership standing of every picture is already established when creating the coaching information for the assault mannequin. This managed setup permits for a transparent evaluation of how successfully the assault mannequin can distinguish between pictures that have been a part of the fine-tuning dataset and people who weren’t.
For these checks, Steady Diffusion V1.5 was used. Although this relatively outdated mannequin crops up lots in analysis because of the want for constant testing, and the in depth corpus of prior work that makes use of it, that is an applicable use case; V1.5 remained in style for LoRA creation within the Steady Diffusion hobbyist neighborhood for a very long time, regardless of a number of subsequent model releases, and even despite the arrival of Flux – as a result of the mannequin is totally uncensored.
The researchers’ assault mannequin was based mostly on Resnet-18, with the mannequin’s pretrained weights retained. ResNet-18’s 1000-neuron final layer was substituted with a fully-connected layer with two neurons. Coaching loss was categorical cross-entropy, and the Adam optimizer was used.
For every take a look at, the assault mannequin was educated 5 instances utilizing totally different random seeds to compute 95% confidence intervals for the important thing metrics. Zero-shot classification with the CLIP mannequin was used because the baseline.
(Please be aware that the unique main outcomes desk within the paper is terse and unusually obscure. Subsequently I’ve reformulated it under in a extra user-friendly vogue. Please click on on the picture to see it in higher decision)

Abstract of outcomes from all checks. Click on on the picture to see increased decision
The researchers’ assault technique proved handiest when focusing on fine-tuned fashions, significantly these educated on a particular set of pictures, corresponding to a person’s face. Nonetheless, whereas the assault can decide whether or not a dataset was used, it struggles to establish particular person pictures inside that dataset.
In sensible phrases, the latter will not be essentially a hindrance to utilizing an method corresponding to this forensically; whereas there’s comparatively little worth in establishing {that a} well-known dataset corresponding to ImageNet was utilized in a mannequin, an attacker on a personal particular person (not a star) will are inclined to have far much less selection of supply information, and want to totally exploit accessible information teams corresponding to social media albums and different on-line collections. These successfully create a ‘hash’ which will be uncovered by the strategies outlined.
The paper notes that one other method to enhance accuracy is to make use of AI-generated pictures as ‘non-members’, relatively than relying solely on actual pictures. This prevents artificially excessive success charges that would in any other case mislead the outcomes.
A further issue that considerably influences detection, the authors be aware, is watermarking. When coaching pictures comprise seen watermarks, the assault turns into extremely efficient, whereas hidden watermarks provide little to no benefit.
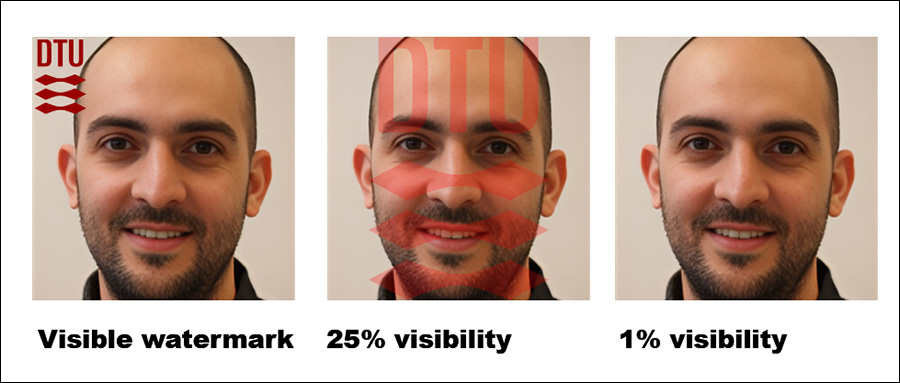
The suitable-most determine exhibits the precise ‘hidden’ watermark used within the checks.
Lastly, the extent of steering in text-to-image era additionally performs a job, with the perfect stability discovered at a steering scale of round 8. Even when no direct immediate is used, a fine-tuned mannequin nonetheless tends to provide outputs that resemble its coaching information, reinforcing the effectiveness of the assault.
Conclusion
It’s a disgrace that this attention-grabbing paper has been written in such an inaccessible method, appropriately of some curiosity to privateness advocates and informal AI researchers alike.
Although membership inference assaults could develop into an attention-grabbing and fruitful forensic instrument, it’s extra vital, maybe, for this analysis strand to develop relevant broad ideas, to forestall it ending up in the identical sport of whack-a-mole that has occurred for deepfake detection on the whole, when the discharge of a more moderen mannequin adversely impacts detection and comparable forensic techniques.
Since there’s some proof of a higher-level tenet cleaned on this new analysis, we are able to hope to see extra work on this path.
First printed Friday, February 21, 2025


